How to quantum secure your business
How to quantum secure your business
Let's play with the idea that some unknown actor has already managed to secretly build a usable quantum computer today – what could it/they actually do? And how serious would this threat be?
The answer is that the consequences would be enormous. Such an actor would not only be able to secretly read almost all the information we send over the internet today. They would also be able to forge almost all digital identities and signatures. So it's not just your private emails or the confidential conversations of decision-makers that would be wide open to reading. The threat also applies to logins to online banks, identification with authorities, signing financial transactions, digital checks of passports and credit cards and more, i.e. large parts of what today builds the foundation of our digital society.
In this text, I will try to break down the issues in a way that is useful for those of you who want to take action and protect your systems and your data against this threat.
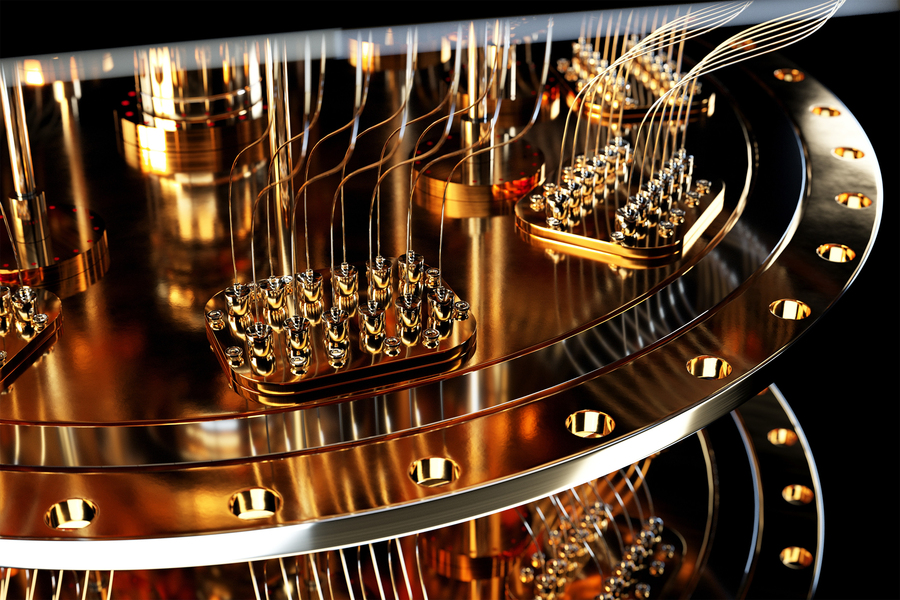
How do quantum computers work and why do they pose a threat?
Quantum computers solve problems in a completely different way than conventional computers. In simple terms, ordinary computers work digitally with weak electrical currents such as zeros and ones, while quantum computers use quantum mechanical states and probability distributions. For the vast majority of problems, quantum computers will always be clumsy, extremely expensive, and inferior to the classical computers we already have today. But for certain specific mathematical problems, we know of algorithms that only work on quantum computers, and that can exploit the hard-to-tamed potential power of quantum computers. Unfortunately, it happens to be the very mathematics that underlies the security of the best and most common algorithms we commonly use today to secure our systems. In practice, this means that quantum computers risk sweeping away the security we have today with standards for encryption and signing such as RSA and Elliptic curves, whose security is based on the fact that it is extremely demanding for ordinary computers to factor very large numbers.
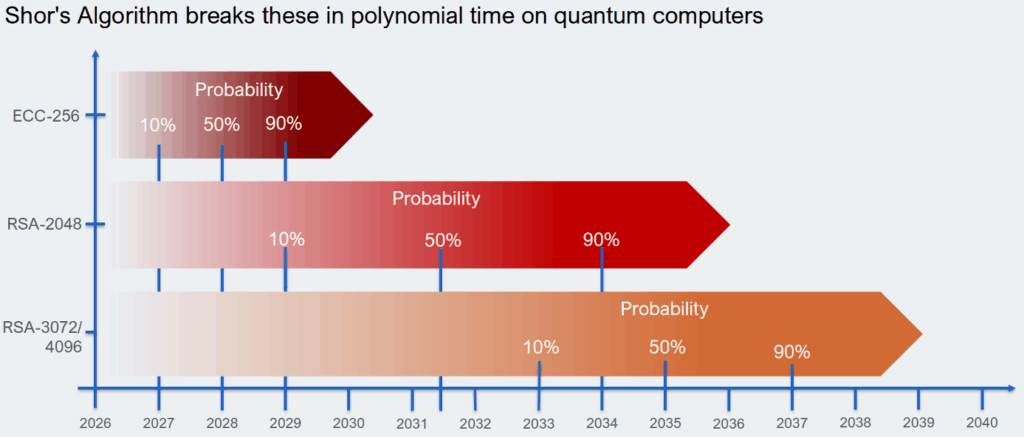
When will quantum computers arrive?
If the threat is so serious, why hasn't everyone already rebuilt systems and algorithms to prevent this? The answer is that there are many different estimates of how far in the future the threat lies. Building a usable quantum computer is an extreme technical challenge, and it is not even certain that they will ever become a real threat. But technology is advancing rapidly, and as always, it is difficult to predict when a new technology will go from Proof of Concept to a working product. In recent years, great progress has also been made on the theoretical side, where it has been possible to optimize the theoretical quantum algorithms in such a way that they could be executed on significantly smaller quantum computers than previously thought. The gap between today's working Proof of Concept and a fully realized threat is narrowing.
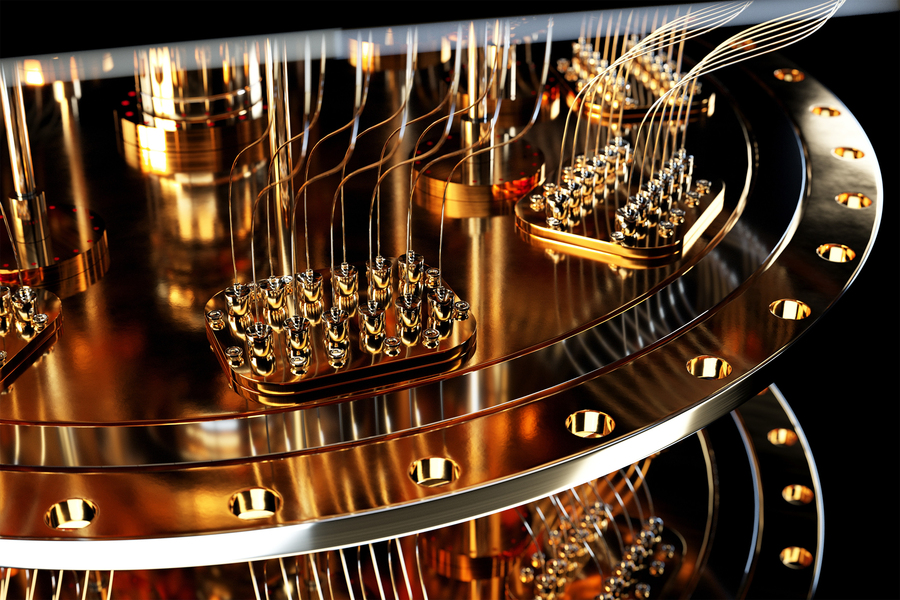
The most optimistic guesses say we could see quantum computers large enough to break the first codes within two years. Others say five to ten years. American National Institute of Standards and Technology (NIST) has set a timeline where our current algorithms will be considered insecure by 2030, and must be completely replaced by 2035. Google have recently announced that they will start requiring post-quantum secured algorithms as early as 2029.
What should I do to quantum secure my business?
The way forward is to switch to new algorithms that are designed based on what we know today to be safe for quantum computers. However, the new algorithms have only recently been standardized, so there is not yet much proven experience on how to implement them. There have also been examples of proposed ”quantum-safe” algorithms that have proven to be relatively easy to crack for conventional computers.
It is therefore a matter of both replacing now and preparing to be more flexible in the future. With all the technological developments, it must be easy to correct, adapt and replace algorithms to maintain security. The two most important things that should be done immediately, or at least as soon as possible, are:
- Inventory
The first thing you need to do is list the algorithms used in the systems. This is a rather tricky task, considering that it also includes all the algorithms that your subcontractors for the systems use. You also need to make sure that you can continuously monitor which algorithms are used. - Build preparedness
Once you have taken stock of the algorithms used in all parts of the systems, you need to make sure they can be replaced and have a plan for how to proceed when the time comes. If you are lucky, a simple reconfiguration will suffice, otherwise you will need to rebuild.
In summary, the uncertainty is now great. Even if the probability of useful quantum computers appearing within one to two years is very small, the consequences would be enormous. Therefore, we must act on the risk now. Waiting and seeing, until the risk suddenly becomes a fact, is downright unwise.
The image shows the current best guess for when quantum computers will be able to break our algorithms. Source: Inéz Atug, RSA Conference 2026
Latest articles



Insights
Latest articles

Speaking of Glasswing: responsible, but not enough

8 principles for building secure systems
